Detection without analysis creates noise, not awareness. Anomaly Federal's intelligence layer processes every incoming sensor feed and observer report into decision-quality information, giving operators confidence-scored, contextualized data that distinguishes a credible threat from a routine overflight. This is where our underlying technology delivers measurable mission value: not as a collection of features, but as outcomes that directly support operational decision-making.
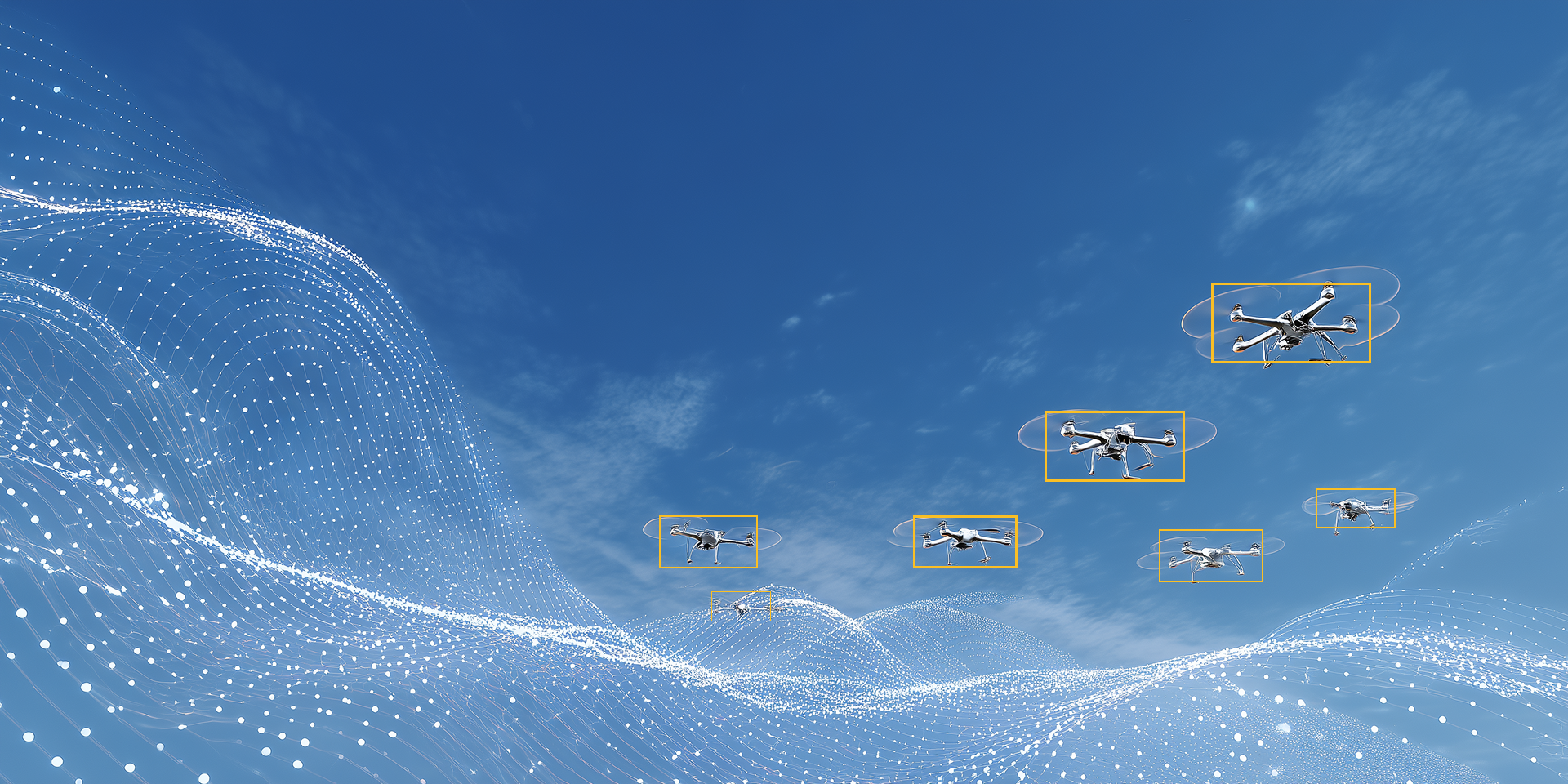
Our computer vision pipeline delivers real-time classification of drones, fixed-wing aircraft, rotary-wing aircraft, birds, and aerial anomalies. Optimized for EO and IR sensors, the system produces confidence-scored identifications with annotated bounding boxes, enabling operators to quickly characterize detected objects without manual review of raw video feeds. The pipeline is designed for deployment across commercial sensor hardware and does not require proprietary optics.
Proprietary multi-sensor triangulation technology synchronizes detections from geographically distributed sensors to reconstruct precise three-dimensional flight paths and airspeed calculations in real time. Built on an Earth-Centered Earth-Fixed coordinate frame with sub-5-meter altitude accuracy, the system produces the positional fidelity required for higher-fidelity threat assessment and supports downstream line-of-sight analysis. The architecture is sensor-agnostic and scales to any number of distributed reporting nodes.

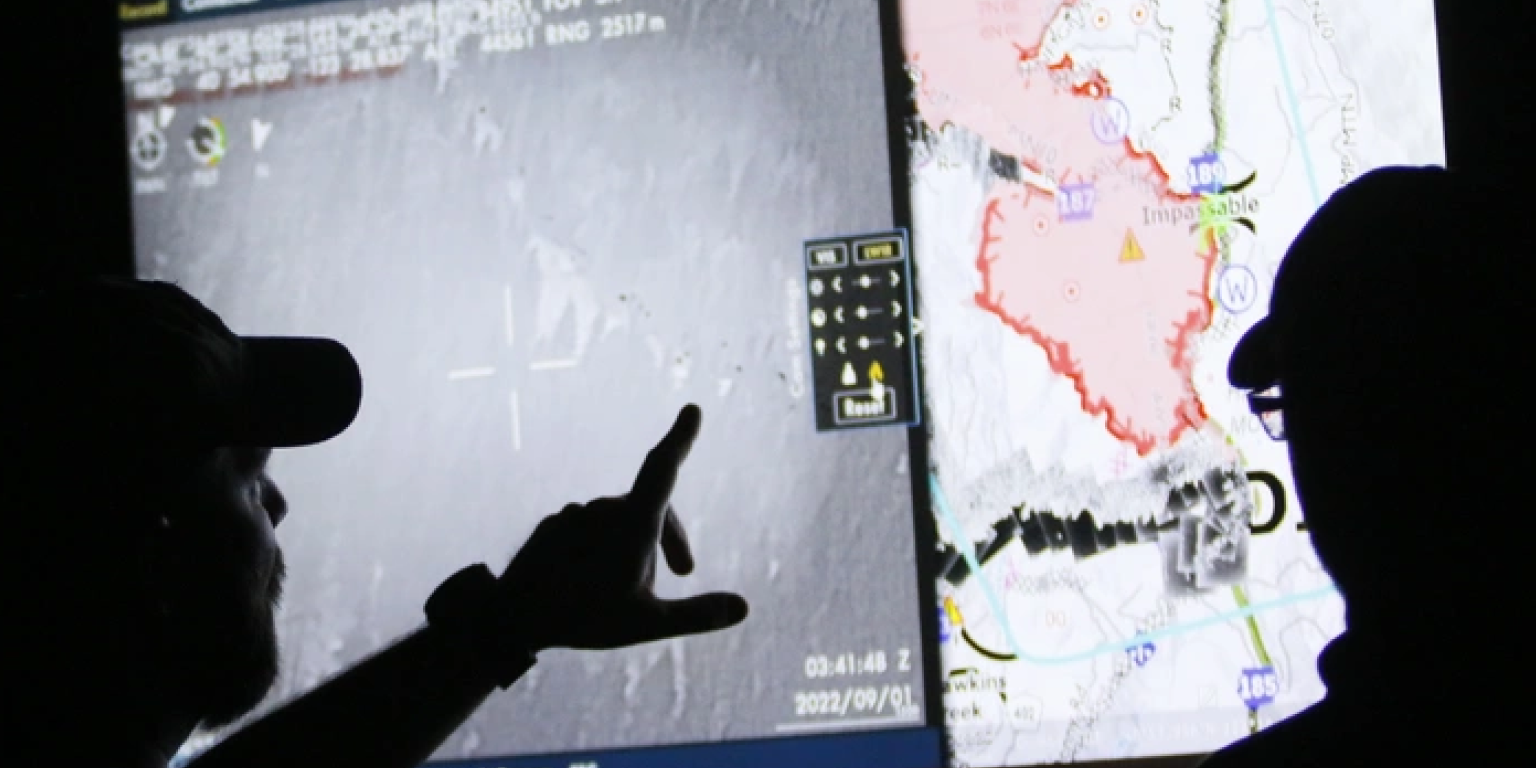
Anomaly Federal's scoring algorithm consolidates behavioral, positional, and contextual factors into a single 0-to-100 threat score per detected object. Scores update continuously as new data is ingested, enabling operators to prioritize response decisions without cognitive overload in high-tempo environments. The methodology is transparent and auditable, supporting chain-of-custody documentation and authority-level reporting requirements.
Operators can query historical aerial activity within any defined geographic boundary, filtering by time range, object type, and behavioral signature. The historical intelligence layer supports pre-mission threat assessments, post-event analysis, and the identification of recurring flight patterns that may indicate surveillance or pre-attack reconnaissance activity. Data exports are compatible with leading external analysis tools and integrate directly with customer C2 systems via unified API.