Intelligence without a response chain is incomplete. Anomaly Federal's action layer closes the loop between detection, analysis, and human decision-making, ensuring that when a threat is identified, designated personnel are notified, equipped with relevant data, and able to act within their established authority structure. Every integration is built for the C2 infrastructure you already own. Anomaly Federal does not create platform lock-in.
When our threat scoring engine flags a potential threat, the alert system activates across the mobile network without requiring manual operator intervention. Nearby observers and designated personnel receive targeted notifications calibrated to the threat score, triggering corroboration and response protocols at the moment they are needed. The system supports geographic targeting for area-specific notifications, configurable threshold-based triggering, and full integration with existing command and control infrastructure via validated API.
Anomaly Federal's augmented reality identification overlay gives field personnel real-time object classification data directly on their mobile or wearable device. When an aerial object is detected in proximity, the AR interface surfaces classification data, confidence scores, and positional information in the operator's field of view. This eliminates the latency of requesting identification support from a command element, compressing the recognition-to-response timeline at the point of contact. The interface operates on standard commercial mobile hardware and requires no specialized equipment.

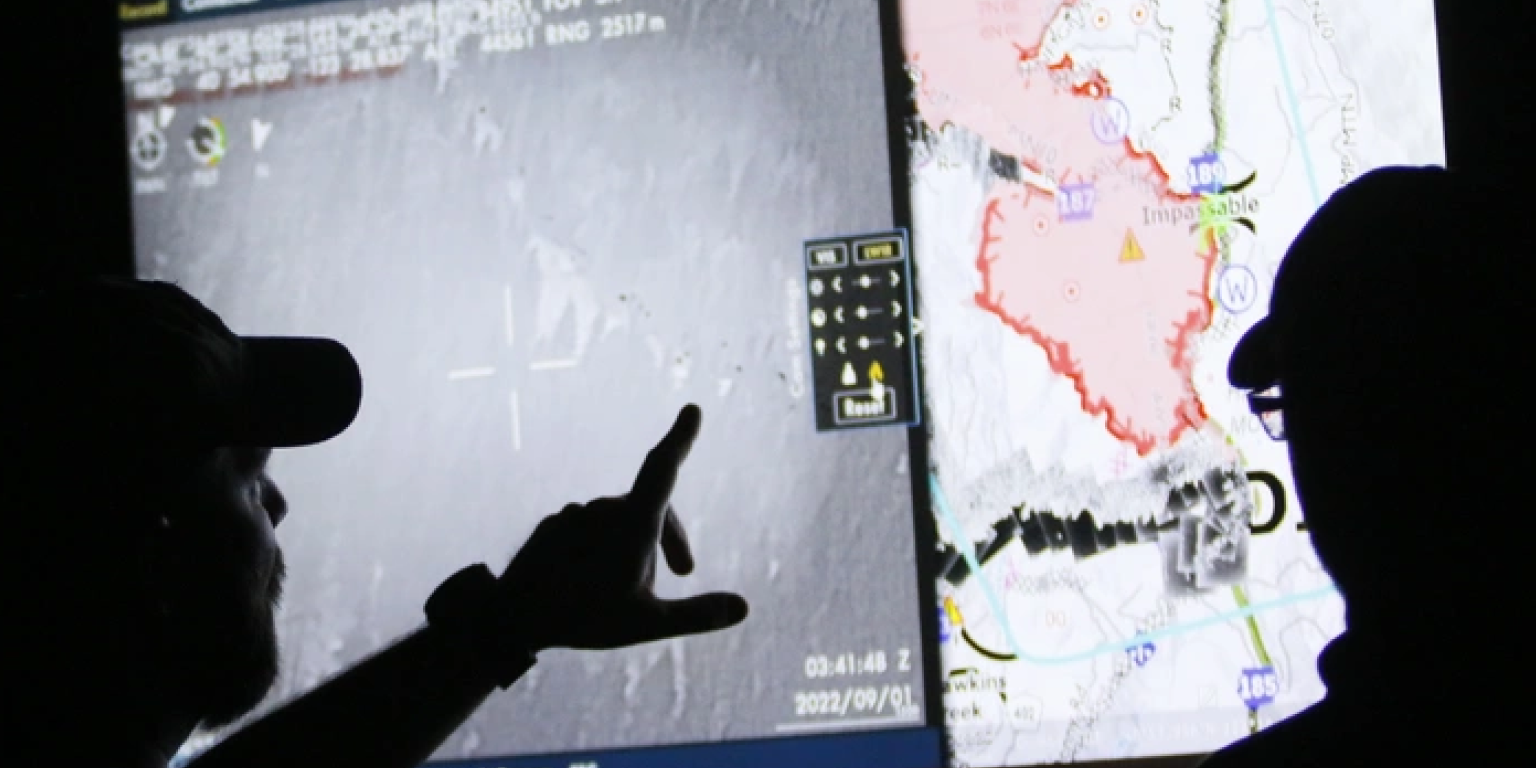
Anomaly Federal is purpose-built for interoperability. Detection data, threat scores, alert records, and historical archives are exposed through a unified API validated through commercial deployment, giving program managers the flexibility to integrate Anomaly Federal outputs into any C2 architecture already in place. Anomaly Federal does not require a proprietary command interface, does not restrict data portability, and does not create dependency on our platform to maintain mission continuity.